
IAM DevOps as-a-Service
Is your Identity and Access Management fit for growth?
The world is turning to digital by default and online business models are rapidly being introduced. Organisations need to deliver new products and services quicker while increasingly being exposed to security risks and becoming victims of cyber crime. In addition, the array of new laws and regulations is causing a heightened compliance risk.
Identity and Access Management (IAM) plays a key role in mitigating the aforementioned risks. Even more, IAM has become an indispensable part of the strategy for conducting business, achieving growth and safeguarding continuity. In our modern world where the only constant is change, companies are now looking for agile IAM delivery. However, IAM is a specialized domain with specific skill sets and resources are scarce.
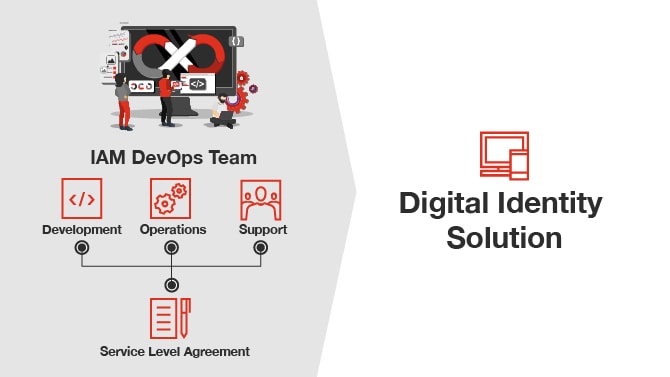
Our IAM DevOps as-a-Service proposition gives you the needed business agility to take care of your Digital Identity solution(s).
Digital Identity as strategic area
PwC has indicated Digital Identity services as one of its strategic areas. PwC founded an EMEA Impact Centre for Digital Identity, which has dedicated research & development as well as business development resources who work across the EMEA region to grow our portfolio of Digital Identity Services in the market as well as perform QA and share best practices and align on strategy in the greater EMEA region. PwC Digital Identity has over 170 Digital Identity specialists of which 50 are located in the Centre of Excellence in the Netherlands.
How can we help?
PwC offers IAM DevOps as-a-Service to provide business agility by combining Plan, Build & Run capabilities in one single team to support organisations to effectively run and enhance their IAM solutions. To make the transition to offering IAM DevOps as-a-Service in your organisation, PwC created a structured approach with a proven methodology. This consists of three stages in which the technical setup takes place, the transition to a DevOps mode after which the full IAM DevOps as-a-Service can be offered. At that point, PwC develops and operates your Identity Solution(s) based on a defined Service Level Agreement.
Benefits of IAM DevOps as-a-Service:
- Business agility - Agile IAM delivery ensures flexibility for your organisation in addressing your digital transformation agenda and it constantly changing business requirements
- Speed of deployments - Continuous Development and dedicated support capacity ensuring faster time to service and resolution of problems
- Stable IAM environment - Due to continuous small improvements which are deployed often and operated by the same team according to best-in-class DevOps practices and technologies
- Low costs - Less overhead and time spent on setting up (change) projects and gathering budget
- Peace of mind - You will receive development, operational and support services from the best IAM experts from a firm with 20+ years of experience in IAM who is recognized as a Leader by the relevant analysts in the cybersecurity world
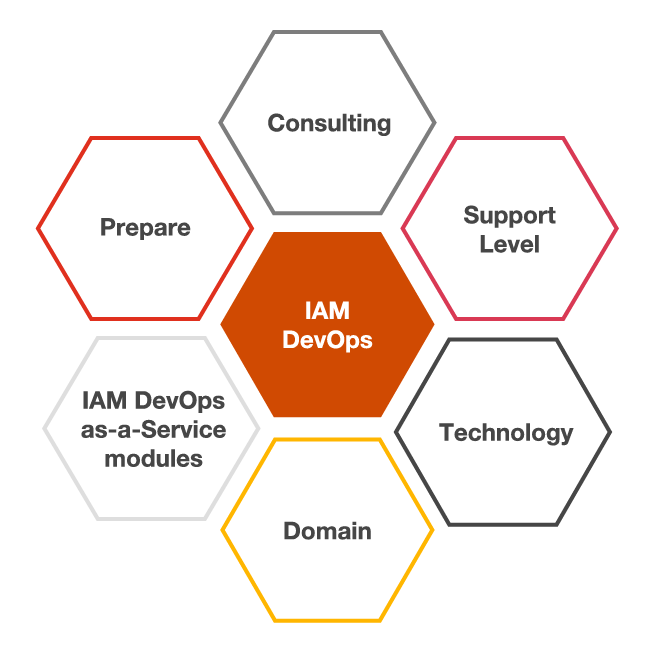
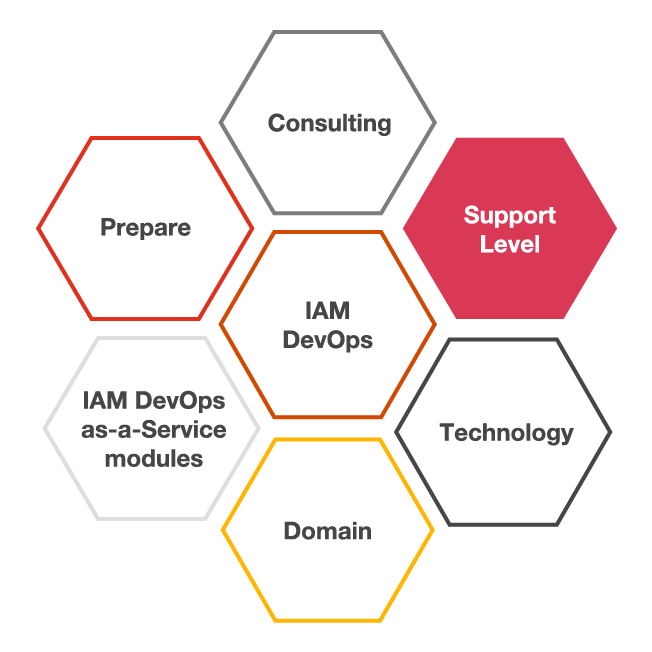
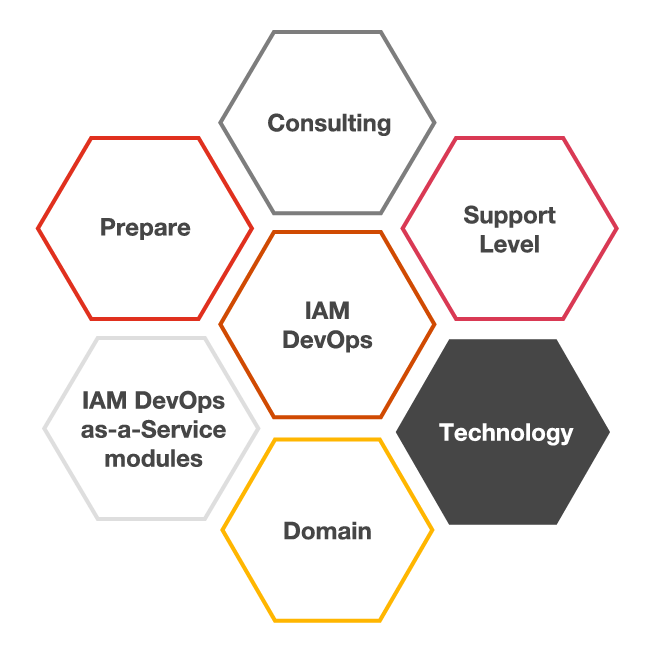
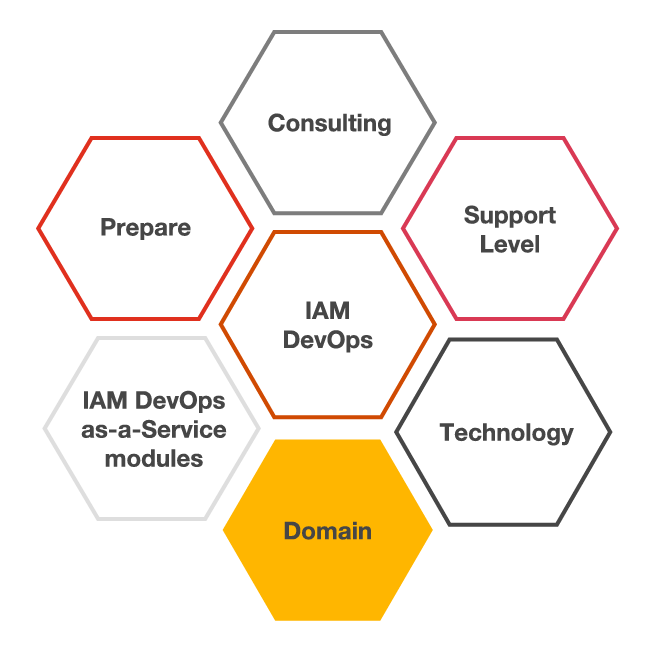
What can we offer?
IAM DevOps as-a-Service is structured into modules. By adding desired support levels, identity domains, technology and consulting services it can be tailored to your needs.
- IAM DevOps
- Prepare
- Consulting
- Support Level
- Technology
- Domain
IAM DevOps
- Development
In relation to the development of the Digital Identity Solution, this means putting work effort towards supplied requirements (user stories) which are top priority on the product development backlog. This work could involve activities like analysing, designing, architecting, programming, configuring, integrating, installing, testing, deploying, documenting, and reviewing these user stories. - Operations
In relation to operating services, this means all scheduled or normal day-to-day activities related to the Digital Identity Solution. This includes deploying new versions and updates to production, doing regular health checks and providing support during all the test stages. This work effort will be done as part of the provided scheduled change capacity that is offered. - Testing & Deployment
We use Best Practices like automation for testing and deploying by making use of CI/CD pipelines. For example, changes are validated through automated test scripts and automated cloud deployment is being done by managed clusters and containerization. - Vendor Management
In case of any incidents with the vendor's software, we will interact with the vendor to escalate and follow incidents. We will proactively work together with the vendor to solve any issues, for example examining log files and applying patches. We also manage the relation over the axes of the contract about new versioning, patches and security updates. - Setup DevOps
Depending on the maturity of DevOps in your organisation, this may involve setting up infrastructure and technology to make sure both the Digital Identity Solution and the supporting technology like clusters and pipelines ready to migrate to DevOps as-a-Service. - Service Management
A service manager manages the continuous delivery, scheduling and reporting of the service. This includes the incident management around the Digital Identity Solution and follow-up to third party Digital Identity vendors.
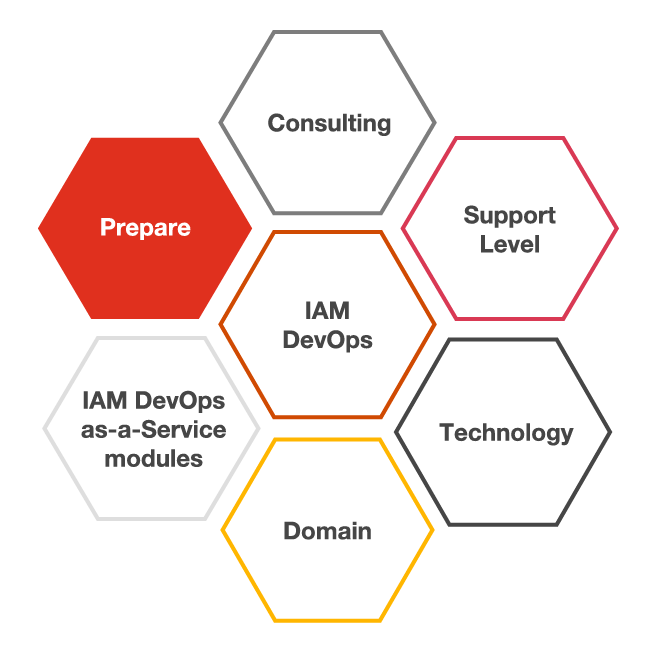
Prepare
- IAM Operating Model
The IAM Target Operating Model clarifies how to make IAM ‘work’ within your organisation. The operating model provides clarification about the required IAM processes to be in place and expresses expectations about how different stakeholders are involved in those processes and their responsibilities. It also highlights how the IAM processes tie in to adjacent non-IAM processes - Architecture & Roadmap
To determine the roadmap, it is important to determine the current state of the architecture and to define the desired state. PwC's Digital Identity team has IT Architects who can guide and support all the steps towards the best roadmap for your Digital Identity Solution and how IAM DevOps as-a-Service can deliver the most value. - Business case
The development of a business case is primarily the development of support for the investment decision. PwC can support in getting all the right stakeholders involved to validate the business case for IAM DevOps. - GAP Analyses
We will perform a gap analysis to gain visibility of the current and desired (IAM) state. We will focus on technology state, data quality, current operating model and processes that can give valuable information to ensure transitioning to DevOps as-a-Service will be frictionless. This input is used to put first activities on the backlog for the next stages.
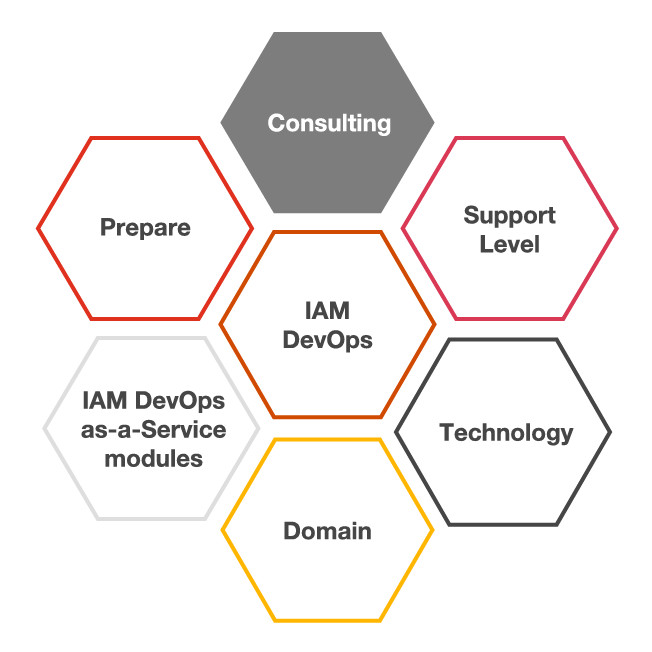
Consulting
- Change Training Communication (CTC)
The CTC Module is an optional module where PwC will take care of Change, Training and Communication efforts for the duration of the continuous improvement of the Digital Identity Solution. Efforts by dedicated CTC consultants will be increased and decreased due to the business change needs and will perform activities like, developing a change and awareness programme, writing end-user documentation, giving end-user training as well as train-the-champion sessions. - Product Owner
The Product Owner is responsible for maximizing the value of both the product and the project team. Typically a client assigns their own Product Owner to be the liaison between the Client organisation and the DevOps team, however It is possible to optionally add an experienced PwC Product Owner to the IAM DevOps team. - Subject Matter Experts
PwC's Digital Identity team offers expert consulting from Subject Matter Experts in a wide variety of fields, such as: IAM Architects, Compliance specialists and PSD2 specialists. These experts can proactively advise the business and product owner on trends and developments in the Digital Identity field.
Support Level
- Support
IAM DevOps as-a-Service offers you various levels of support. Depending on your requirements and needs, we offer the choice to choose between Service Levels. Considering your digital identity solution is mission critical, we offer 24/7 support with a < 1 hour response time. The scope of supporting services are described in the Service Level Agreement. - Monitoring Integration
We offer integration with your monitoring solution. Our applications are exposing (for example) Prometheus metrics to enable monitoring on the IAM stack. This allows us to provide proactive support and provide valuable business insights if integrated with monitoring tools such as Prometheus. In addition, it allows for alerts to be sent directly to the IAM DevOps team. The team will then be alerted and can proactively take measures. - Uptime Agreement
As a separate module we can also add uptime targets to the Service Level Agreement of the Digital Identity Solution. - Service Desk
Preferably our Digital Identity services team integrates with your service desk for first line support, however we can also provide you with a Service Desk that can act as a first point of engagement between your users and the Digital Identity Solution.
Technology
- Licenses
PwC can support in dealing with software vendors and necessary licenses. We will keep track on what type and the number of licenses needed. We also do the negotiations and keep contact with the software vendor's account managers to ensure you get the most value out of the used IAM products. - Platform
At this stage PwC will develop, operate and support the Digital Identity Solution on your platform, we can refer you to vendors that can provide you with many of our supported platforms or you can host the platform yourself. market leading cloud and on-premise platforms for DevOps are supported.
Domain
- Customers Identity and Access Management (CIAM)
CIAM plays a key role in the interaction with end users and their access to information assets. CIAM requires continuous development and attention as it touches the core of an organisation’s business. When the solution is down, not secure enough, or lacks the right user experience the business will be impacted. Our service offers you the agility to quickly respond and focus on those issues that need your immediate attention. - Identity Governance & Administration (IGA)
In recent years, the requirements placed on IGA tools have grown exponentially. Organisations grow fast and furiously whilst their enterprise applications extend further into the mobile and cloud space. It is therefore becoming increasingly important that an organisations' IGA solution does not hinder it, but rather grows with it, seamlessly supporting its success while providing flexibility and agility. - Privileged Access Management (PAM)
A PAM solution delivers an enterprise service which enforces a governance framework and operational procedures. This concerns the accounts with the highest privileges to control systems, applications, databases and devices. It also Includes accounts which have access to sensitive data, that if compromised, has the potential to cause significant damage to the organisation. Considering modern agile development methodologies, it is important that you have the agility to act fast on controlling privileged access. - Internet of Things (IoT)
Everyday objects are becoming an entity on the Internet. These objects have the ability to interact with both people and other objects, and can make autonomous decisions based on these interactions. As these can be considered as a fast growing number of identities to be managed, you need the agility of an IAM solution to support this growth.
Why PwC?
When it comes to finding powerful solutions to complex problems, few organisations have a stronger track record than PwC. For over five decades and across 158 countries, we have used our experience, reach and resources to raise the bar continuously.
- PwC’s global team of over 650 IAM professionals are part of a larger team of 3,500 cybersecurity and privacy SMEs.
- The team includes specialized consultants, architects and engineers next to intelligence analysts, cyber-forensics investigators, attorneys and consultants as well as industry SMEs.
- 20+ years of experience helping businesses across industries strategically assess, design, deploy, improve and run cybersecurity and IAM programs and solutions.
- PwC’s EMEA Digital Identity practice is headquartered in Amsterdam and hosts its centre-of-excellence there.
















